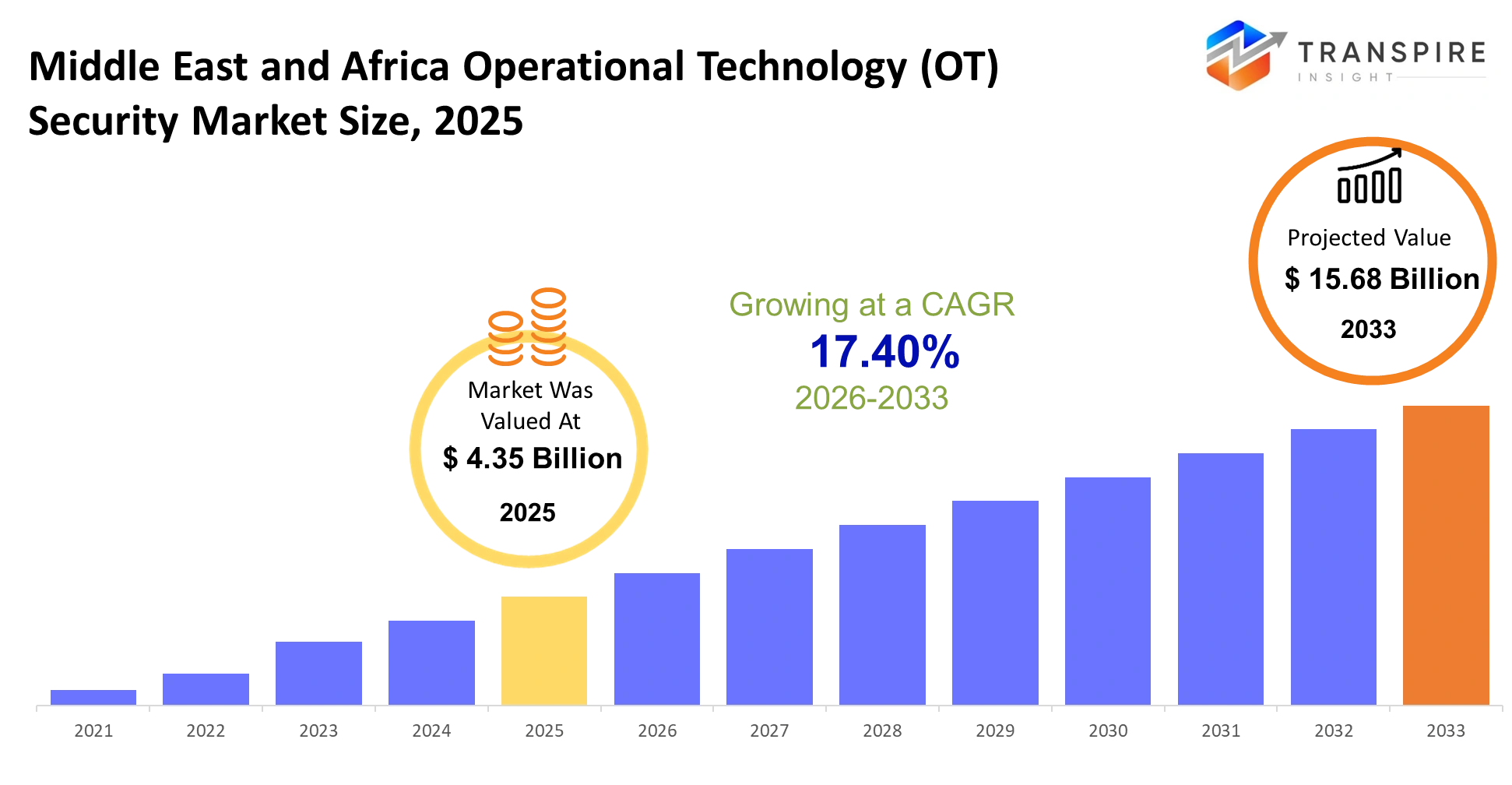
Middle East and Africa Operational Technology (OT) Security Market Size & Forecast:
- Middle East and Africa Operational Technology (OT) Security Market Size 2025: USD 4.35 Billion
- Middle East and Africa Operational Technology (OT) Security Market Size 2033: USD 15.68 Billion
- Middle East and Africa Operational Technology (OT) Security Market CAGR: 17.40%
- Middle East and Africa Operational Technology (OT) Security Market Segments: By Component (Hardware, Software, Services), By Security Type (Network, Endpoint, Application, Cloud), By Application (Energy, Manufacturing, Utilities, Oil & Gas), By End-User (Industrial Enterprises, Utilities, Oil & Gas Firms, Government)
To learn more about this report, Download Free Sample Report
Middle East and Africa Operational Technology (OT) Security Market Summary:
The Middle East and Africa Operational Technology (OT) Security Market size is estimated at USD 4.35 Billion in 2025 and is anticipated to reach USD 15.68 Billion by 2033, growing at a CAGR of 17.40% from 2026 to 2033. The OT security market in the Middle East and Africa (Saudi Arabia, UAE, South Africa, and the Rest of Middle East and Africa) will operate in the context of the larger industrial cybersecurity marketplace, fueled by the growth of the digital ecosystem in the region along with increasing vulnerabilities to cyberattacks against key targets. The need for enhanced OT security will be high among energy companies, utility organizations, and transportation organizations due to more aggressive and disruptive forms of cyberattack. Increased pressure from government agencies in Saudi Arabia and the UAE will drive tougher regulations regarding cybersecurity.
Key Market Trends & Insights:
- Industrial systems are shifting from isolated setups to connected networks, increasing exposure to cyber threats and driving the need for continuous security monitoring—especially in critical sectors like energy and utilities.
- Adoption of cloud-based and hybrid security solutions will grow, allowing sensitive operations to stay offline while leveraging cloud capabilities for broader monitoring and management.
- Governments, particularly in Saudi Arabia and the UAE, will introduce stricter, sector-specific cybersecurity regulations, pushing organizations toward better auditability, compliance, and transparency.
- In South Africa, the focus will be on practical implementation of cybersecurity measures despite operational and resource challenges.
- A shortage of skilled cybersecurity professionals will lead to higher reliance on managed security services and automation, with vendors offering simplified platforms that reduce the need for large in-house teams.
Middle East and Africa Operational Technology (OT) Security Market Segmentation
By Component
Hardware- In this regard, hardware will consist of secure gateways, industrial firewalls, and embedded protection hardware that will be built-in directly into control systems. The organizations will depend on these hardware layers in protecting their machinery from any potential risks coming from outside. There will be an increasing demand for the use of this hardware since the old legacy infrastructure will be replaced by newer technology that supports the use of security-related features in tough working conditions.
Software- The software in this case will target the detection and identification of possible threats and vulnerabilities in the industrial system. There will be a greater need for software solutions that have the ability to give the organization predictive insights and detect abnormal activities within the system to prevent any future interruptions.
Services- The services required will consist of consulting, system integration, and managed security services. Many organizations will depend on these services because there will be many cases where they will need external support due to inadequate skills and experience in handling such matters.
To learn more about this report, Download Free Sample Report
By Security Type
Network- Network security will remain important for industrial systems because their interconnections continue to increase. The solutions will track network traffic between control systems and external networks which will identify unauthorized access through detected anomalies. Organizations will implement segmentation strategies to prevent attack propagation while protecting essential operations from access to less secure areas.
Endpoint- Endpoint security will protect devices which include programmable logic controllers and sensors and operator workstations. The growing intelligence and connectivity of these endpoints will make them into prime targets for cyberattacks. Companies will deploy lightweight protection solutions which protect devices while maintaining their operational efficiency throughout industrial activities.
Application- The growing popularity of industrial software platforms will create a greater need for application security because these platforms will offer advanced features and improved network connectivity. Organizations will work to secure supervisory control and data acquisition systems and other critical applications from exploitation. The development of secure operational workflows will require organizations to concentrate on three areas: testing procedures and patch management and secure coding methods.
Cloud- The industrial sector will increase its adoption of cloud security solutions because more industrial data will be transferred to remote platforms for analysis and storage. Companies will use secure access controls and encryption methods and monitoring solutions to safeguard their classified operational data. Organizations will implement this transition to demonstrate their growing trust in cloud technologies while implementing rigorous security measures for essential systems.
By Application
Energy- The energy sector requires strong security measures because it protects essential national infrastructure systems. The power generation and distribution networks will implement modern tracking systems which will enable them to identify threats and take immediate action. The security resources will be allocated to prevent interruptions which endanger the safety of numerous people and the economic functioning of societies.
Manufacturing- The digital transformation of manufacturing facilities requires security protection for their automated production lines. The increasing deployment of robotic systems together with interconnected machinery will create a greater requirement for secure system communication. Organizations will use proactive threat detection systems to achieve their goal of decreasing operational interruptions while their business activities continue undisturbed.
Utilities- Utilities will protect their water and electricity systems together with their waste management services against cyber threats. The digitization of these services requires organizations to establish methods for providing safe uninterrupted service delivery. Operators will implement multiple security protection systems to secure their existing systems and their new networked resources which operate throughout extensive areas.
Oil & Gas- Oil and gas operations require complete security measures because they operate in multiple locations which present significant danger. Protection methods must secure all systems from exploration sites to refineries against attacks which aim to disrupt operations and endanger employee safety. The funding will support the development of remote monitoring systems and secure communication networks and quick response systems for emergencies.
By End-User
Industrial Enterprises- Industrial enterprises will adopt comprehensive security strategies to protect their operational ecosystems which require complete operational protection. The organization will implement cybersecurity measures throughout its operational activities to protect production efficiency. The need for complete asset tracking will intensify in tandem with the increasing use of digital tools because organizations need to manage their risks.
Utilities- Utility providers will strengthen their defenses to ensure uninterrupted public services. The organization will experience greater cyber threats because of its increased digital system integration. The organization will direct its financial resources toward establishing monitoring systems which will help them achieve regulatory compliance and develop systems for quick restoration of essential service networks to maintain trust and operational continuity.
Oil & Gas Firms- Oil and gas companies will implement security measures to protect their most valuable assets and their operations which take place in remote locations. The organization will establish advanced detection systems and secure communication networks to protect its operations at multiple locations around the world. The organization will implement measures that prevent disruptions which would endanger production processes and safety measures and environmental protection efforts.
Government- Government bodies will play a key role in securing critical infrastructure by setting policies and supporting national cybersecurity initiatives. The organization will spend resources to safeguard public sector industrial systems while partnering with private entities to build resilience throughout their operations. The organization will focus on three main areas which include preparedness activities and coordination efforts and infrastructure protection strategies which extend through multiple years.
Regional Insights
The industrial cybersecurity priorities of Saudi Arabian organizations will follow their national transformation programs which focus on digital infrastructure and energy sector modernization. Organizations will invest in securing interconnected operational systems as smart facilities expand. The regulatory framework will provide better guidance which will lead to companies developing standardized protocols that all sectors can use. The organization will focus on protecting vital resources from operational interruptions while it works to achieve economic growth and technological self-sufficiency.
The United Arab Emirates will position itself as a regional leader in advanced industrial security adoption. Companies will develop protection systems because of the fast development of smart cities and automated systems in the utility and transportation sectors. The public and private sectors will work together to establish stronger mechanisms for sharing intelligence about threats. Businesses will search for adaptable solutions which enable them to operate in innovative environments while protecting their critical business operations.
South Africa will implement its industrial security framework by searching for solutions which combine system upgrades with its current infrastructure issues. The facilities must upgrade their systems because their existing cybersecurity practices do not meet current security standards. Local industries will choose affordable solutions which deliver dependable performance without interrupting their production processes. The business world will acquire better understanding about operational risks which will result in businesses implementing monitoring systems and strategies that improve their defense capabilities.
However, in other areas of the Middle East and Africa, adoption will depend on the level of economic growth and development within the regions. In developing nations, efforts geared towards improving security frameworks will be seen as more companies adopt digitalization in industries such as the energy sector, mining, and utilities. International cooperation will help in transferring technologies for these purposes.
Recent Development News
In December 2025, across the Middle East, companies will increasingly adopt AI-led security frameworks to counter advanced cyber threats. A partnership between SentinelOne and Rilian Technologies will enable autonomous defense systems for governments and critical industries. This shift will reflect rising demand for intelligent monitoring solutions capable of handling complex and large-scale industrial environments.
In October 2025, the region will witness growing concern over sophisticated cyberattacks, especially those powered by artificial intelligence. In Saudi Arabia, heightened investment will be directed toward defending critical sectors as digital adoption expands. At the same time, manufacturing industries across the broader region will remain key ransomware targets, reinforcing the urgency for stronger operational security frameworks.
|
Report Metrics |
Details |
|
Market size value in 2025 |
USD 4.35 Billion |
|
Market size value in 2026 |
USD 5.1 Billion |
|
Revenue forecast in 2033 |
USD 15.68 Billion |
|
Growth rate |
CAGR of 17.40% from 2026 to 2033 |
|
Base year |
2025 |
|
Historical data |
2021 – 2024 |
|
Forecast period |
2026 – 2033 |
|
Report coverage |
Revenue forecast, competitive landscape, growth factors, and trends |
|
Country scope |
Middle East and Africa (Saudi Arabia, United Arab Emirates, South Africa, Rest of Middle East and Africa) |
|
Key company profiled |
Siemens, Schneider Electric, Honeywell, Cisco, IBM, Microsoft, ABB, Rockwell, Palo Alto Networks, Fortinet, Check Point, Dragos, Nozomi Networks, Darktrace, Kaspersky |
|
Customization scope |
Free report customization (country, regional & segment scope). Avail customized purchase options to meet your exact research needs. |
|
Report Segmentation |
By Component (Hardware, Software, Services), By Security Type (Network, Endpoint, Application, Cloud), By Application (Energy, Manufacturing, Utilities, Oil & Gas), By End-User (Industrial Enterprises, Utilities, Oil & Gas Firms, Government) |
Key Middle East and Africa Operational Technology (OT) Security Market Company Insights
The important vendors that will operate in OT security for MEA will include major industrial vendors like Siemens, Schneider Electric, Honeywell, and ABB as well as local vendors like Solutions by STC and MEEZA. Such vendors will concentrate on providing their customers with an integrated platform as well as increasing their partnerships for meeting the growing need for OT security.
Company List
- Siemens
- Schneider Electric
- Honeywell
- Cisco
- IBM
- Microsoft
- ABB
- Rockwell
- Palo Alto Networks
- Fortinet
- Check Point
- Dragos
- Nozomi Networks
- Darktrace
- Kaspersky
Middle East and Africa Operational Technology (OT) Security Market Report Segmentation
By Component
- Hardware
- Software
- Services
By Security Type
- Network
- Endpoint
- Application
- Cloud
By Application
- Energy
- Manufacturing
- Utilities
- Oil & Gas
By End-User
- Industrial Enterprises
- Utilities
- Oil & Gas Firms
- Government
Frequently Asked Questions
Find quick answers to common questions.
The Approximate Middle East and Africa Operational Technology (OT) Security Market size for the Market will be USD 15.68 Billion in 2033.
Key Segments for the Middle East and Africa Operational Technology (OT) Security Market By Component (Hardware, Software, Services), By Security Type (Network, Endpoint, Application, Cloud), By Application (Energy, Manufacturing, Utilities, Oil & Gas), By End-User (Industrial Enterprises, Utilities, Oil & Gas Firms, Government).
Major Players in the Middle East and Africa Operational Technology (OT) Security Market are Siemens, Schneider Electric, Honeywell, Cisco, IBM, Microsoft, ABB, Rockwell, Palo Alto Networks, Fortinet, Check Point, Dragos, Nozomi Networks, Darktrace, Kaspersky.
The Current Middle East and Africa Operational Technology (OT) Security Market size is USD 4.35 Billion in 2025.
The Middle East and Africa Operational Technology (OT) Security Market CAGR is 17.40%.
- Siemens
- Schneider Electric
- Honeywell
- Cisco
- IBM
- Microsoft
- ABB
- Rockwell
- Palo Alto Networks
- Fortinet
- Check Point
- Dragos
- Nozomi Networks
- Darktrace
- Kaspersky
Recently Published Reports
-
Apr 2026
3D Optical Profiler Market
3D Optical Profiler Market Size, Share & Analysis Report By Type (Desktop 3D Optical Profiler, and Portable 3D Optical Profiler), By Technology (Confocal Technology, and White Light Interference), By End-Use Industry (Manufacturing, Research Institutions, Automotive, Aerospace and Defense, Medical Devices, and Other), and Geography (North America, Europe, Asia-Pacific, Middle East and Africa, South and Central America), 2021 - 2031
-
Apr 2026
Depth Sensor Market
Depth Sensor Market Size, Share & Analysis Report By Type (Infrared Depth Sensors, Time-of-Flight (ToF) Sensors, Stereo Vision Sensors, Structured Light Sensors, Ultrasonic Depth Sensors), By Application (Automotive, Robotics, Gaming, Consumer Electronics, Industrial Automation, Healthcare, Security & Surveillance, Others), By End Users (Automotive Manufacturers, Consumer Electronics Companies, Healthcare Providers, Industrial Companies, Security Agencies, Gaming Companies, Robotics Companies, Others), and Geography (North America, Europe, Asia-Pacific, Middle East and Africa, South and Central America), 2021 – 2031
-
Apr 2026
Digital Manufacturing Market
Digital Manufacturing Market Size, Share & Analysis Report By Component (Hardware, Software, and Services), By Technology (Robotics, 3D Printing, Internet of Things (IoT), and Others), By Application (Automotive and Transportation, Aerospace and Defense, Consumer Electronics, Industrial Machinery, and Others), By Process Type (Computer-Based Designing, Computer-Based Simulation, Computer 3D Visualization, Analytics, and Others), and Geography (North America, Europe, Asia-Pacific, Middle East and Africa, South and Central America), 2021 – 2031
-
Apr 2026
Digital Visa Services Market
Digital Visa Services Market Size, Share & Analysis Report By Type (Individual Travelers, Group Travelers), By Application (Tourism, Business Travel, Others), and Geography (North America, Europe, Asia-Pacific, Middle East and Africa, South and Central America), 2021 – 2031